Information security reports are a critical component of any organization's risk management strategy. They provide a detailed account of security incidents, vulnerabilities, and preventative measures, ultimately demonstrating due diligence and accountability. A well-structured Information Security Report Template ensures that key information is captured, analyzed, and communicated effectively to stakeholders. This template serves as a foundational document, streamlining the reporting process and promoting continuous improvement in security posture. The core purpose of this report is to clearly articulate the events, their impact, and the steps taken to mitigate them. It's not just a record of incidents; it's a roadmap for preventing future occurrences. A robust Information Security Report Template is an investment in protecting your organization's assets and reputation. It's a vital tool for demonstrating compliance with regulations and industry best practices. This template provides a framework for comprehensive reporting, ensuring consistent and accurate information delivery. Understanding the importance of a well-crafted report is paramount for any organization serious about safeguarding its data and systems. The effectiveness of an Information Security Report Template hinges on its clarity, thoroughness, and adherence to established best practices. It's a dynamic document, requiring regular updates and revisions to reflect evolving threats and organizational changes. A proactive approach to template creation and maintenance is essential for maintaining a strong security culture. Ultimately, a clear and documented incident response process, supported by a comprehensive report, is the cornerstone of effective security.
Section 1: Incident Overview
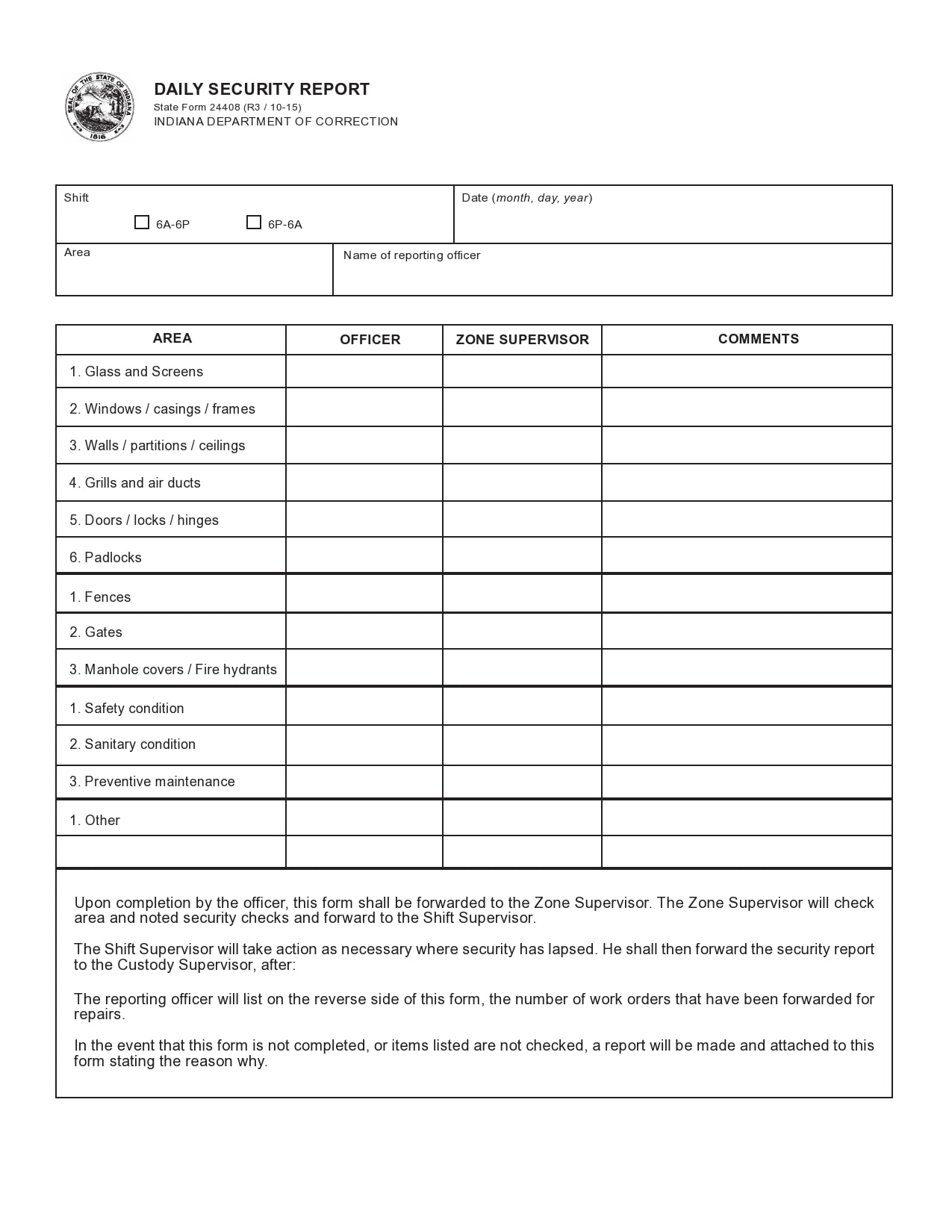
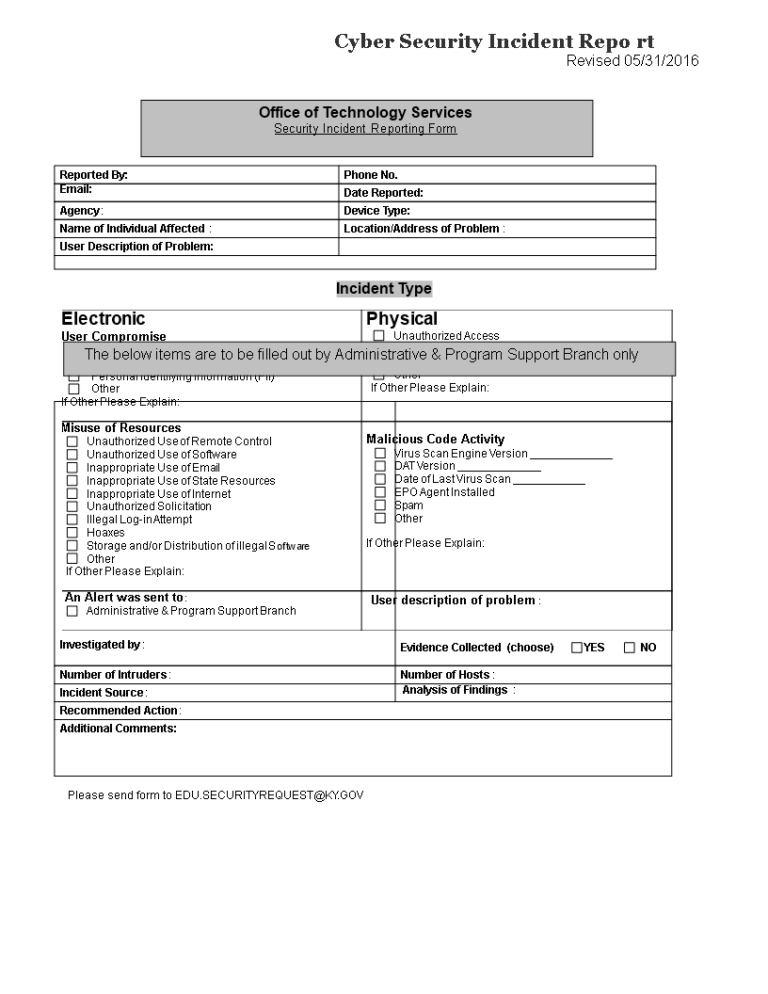
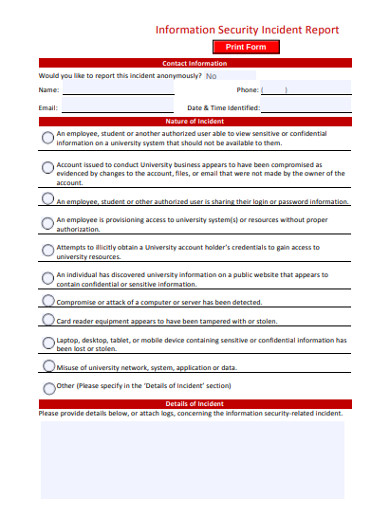
The initial phase of any Information Security Report Template involves a detailed overview of the incident itself. This section captures the core details of the event, providing a chronological account of what happened. It's crucial to avoid speculation and focus on factual observations. The objective here is to establish a clear timeline and understand the scope of the incident. This initial assessment helps to determine the potential impact and informs subsequent analysis. Consider including information such as the date and time of the incident, the location, the affected systems, and the individuals involved. A concise description of the incident's nature – whether it was a phishing attack, a malware infection, or a data breach – is essential. Furthermore, documenting the initial response actions taken is vital. This section should be easily accessible for review by investigators and stakeholders. Proper documentation of the incident's initial response is critical for understanding the root cause and preventing recurrence. A well-documented incident overview provides a solid foundation for subsequent analysis and remediation efforts. This initial phase is often the most challenging, requiring meticulous attention to detail.
Section 2: System Impact and Damage Assessment
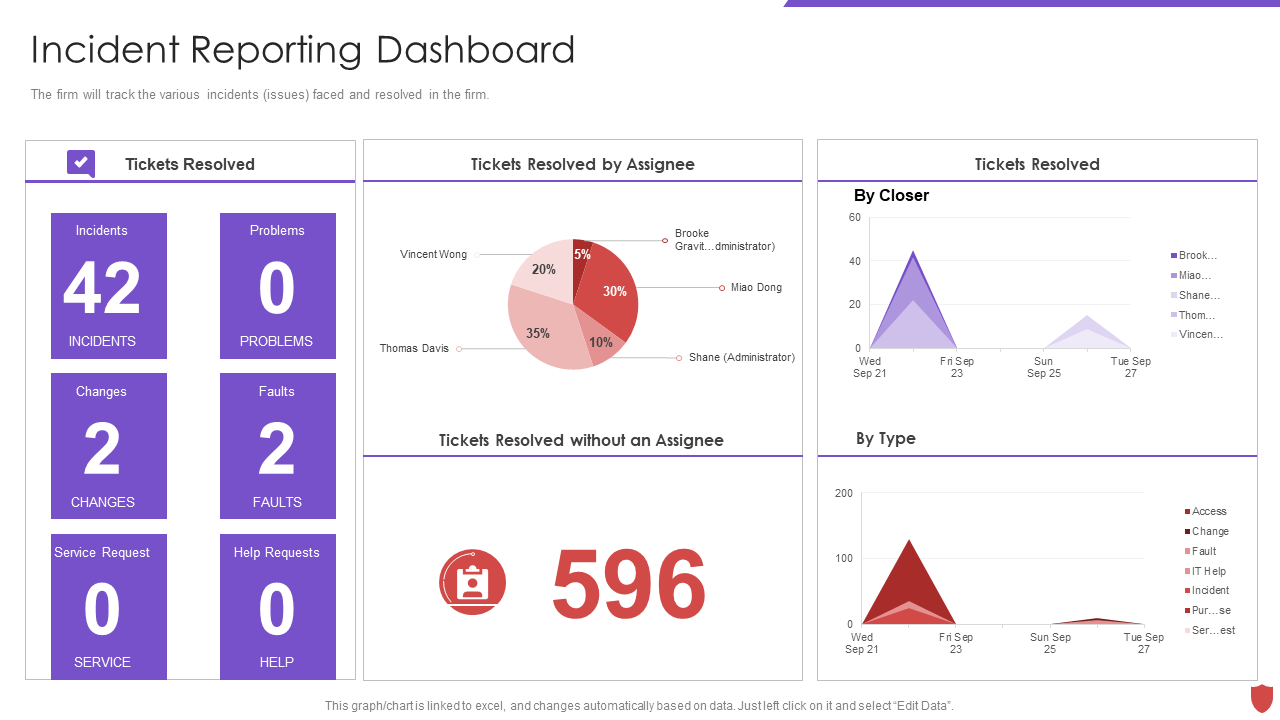
This section delves into the specific systems and data affected by the incident. It provides a granular assessment of the damage caused, quantifying the impact where possible. This includes identifying which systems were compromised, the extent of data loss or corruption, and any operational disruptions. Using standardized metrics, such as downtime hours, data volume affected, and business impact, allows for objective evaluation of the incident's severity. It's important to categorize the impact based on the criticality of the affected systems. For example, a critical server experiencing a complete outage would be classified as a higher-impact incident than a minor data loss affecting a single file. Detailed technical information, such as error messages, logs, and forensic evidence, should be included. Consider using a standardized incident severity scale to consistently categorize incidents. This allows for a comparable assessment across different incidents and facilitates informed decision-making. Furthermore, documenting the steps taken to contain the damage and restore systems is crucial. This section should include details about backups, recovery procedures, and any temporary workarounds implemented.
Section 3: Root Cause Analysis
Identifying the root cause of the incident is a critical step in preventing future occurrences. This section explores the underlying factors that led to the incident, examining potential vulnerabilities, weaknesses in security controls, and human error. A thorough root cause analysis should consider a range of possibilities, including technical flaws, operational deficiencies, and insufficient security awareness. It's important to avoid blaming individuals; instead, focus on identifying systemic issues that contributed to the incident. Techniques such as the 5 Whys or Fishbone diagrams can be helpful in uncovering the root cause. Documenting the identified root cause, along with proposed remediation steps, is essential for driving continuous improvement. This section demonstrates a commitment to learning from past incidents and implementing preventative measures. A proactive approach to root cause analysis is far more effective than simply reacting to incidents after they occur. Analyzing the incident's root cause allows for a more targeted and effective response.
Section 4: Remediation and Recovery
This section outlines the actions taken to remediate the incident and restore affected systems and data. It details the steps taken to address the vulnerabilities that were exploited, implement security controls, and restore services. This includes patching systems, strengthening access controls, enhancing monitoring, and implementing additional security measures. It's important to clearly document the specific actions taken, the resources utilized, and the timelines for completion. For example, detailing the deployment of a security patch, the configuration of new firewall rules, or the implementation of multi-factor authentication. Recovery procedures should be clearly defined and tested. This section should include details about data restoration, system verification, and ongoing monitoring. It's crucial to ensure that systems are fully recovered and that no vulnerabilities remain. A well-documented remediation plan demonstrates a commitment to restoring normal operations and minimizing the impact of the incident. Regularly reviewing and updating the remediation plan is essential.
![]()
Section 5: Lessons Learned and Recommendations
The final section of the Information Security Report Template focuses on lessons learned and recommendations for improvement. It summarizes the key takeaways from the incident, highlighting both successes and failures. This section should provide actionable recommendations for strengthening security controls, improving incident response procedures, and enhancing security awareness. It's important to avoid simply repeating the incident details; instead, focus on identifying areas for improvement. This section should include specific, measurable, achievable, relevant, and time-bound (SMART) goals. For example, "Implement a new vulnerability scanning program within 3 months." The recommendations should be prioritized based on their potential impact and feasibility. Furthermore, the report should consider the role of human factors in security incidents. Identifying and addressing human error is crucial for preventing future occurrences. This section demonstrates a commitment to continuous improvement and a proactive approach to security. A comprehensive Lessons Learned and Recommendations section is a valuable tool for organizational learning and development.
Conclusion
Information Security Report Templates are indispensable tools for organizations seeking to proactively manage their security risks. By providing a structured and comprehensive framework for documenting security incidents, the template facilitates effective communication, analysis, and remediation. The consistent application of a well-crafted template, coupled with a commitment to continuous improvement, is essential for maintaining a strong security posture. The ability to quickly and accurately assess and respond to security incidents is paramount in today's threat landscape. Investing in a robust Information Security Report Template is an investment in the long-term security and resilience of your organization. Ultimately, a proactive and documented approach to security is the most effective defense against evolving threats. The template's adaptability, allowing for customization to specific organizational needs, further enhances its value. Regularly reviewing and updating the template ensures it remains relevant and effective in a constantly changing environment. The importance of a clear and documented incident response process, supported by a comprehensive report, cannot be overstated. A well-executed Information Security Report Template is a cornerstone of a successful security program.
0 Response to "Information Security Report Template"
Posting Komentar